The Commport VAN is privately owned and operated, with established relationships and interconnects with all major VAN service providers, which enables us to forward your documents without delays or additional costs.

SFTP can securely transfer files large and small, over the internet. It builds on the File Transfer Protocol (FTP) and includes Secure Shell (SSH) security components.
FTP enables connectivity via a TCP/IP network. FTP is one of the oldest, most highly used, and most well-proven communications protocols.
AS2 stands for Applicability Statement 2 and it is one of the most popular methods for transporting B2B EDI documents from one organization to another.
Commport offers a secure and dedicated mailbox for each client which can be used to send and receive EDI messages 24/7.
Rely on Commport for all your communications requirements!
Your varied trading partners may require the use of an array of communications options; FTP, AS2, SFTP, VAN. Partnering with Commport enables you to focus on your business, leaving the technical communications to experts in that field: Commport.
Commport can establish a single connection between you and the Commport Network and then Commport can manage all connectivity with your partners. This enables you to rely on one proven connection while also responding to and supporting your trading partners’ various requirements.
Commport offers a secure and dedicated mailbox for each client which can be used to send and receive EDI messages 24/7.
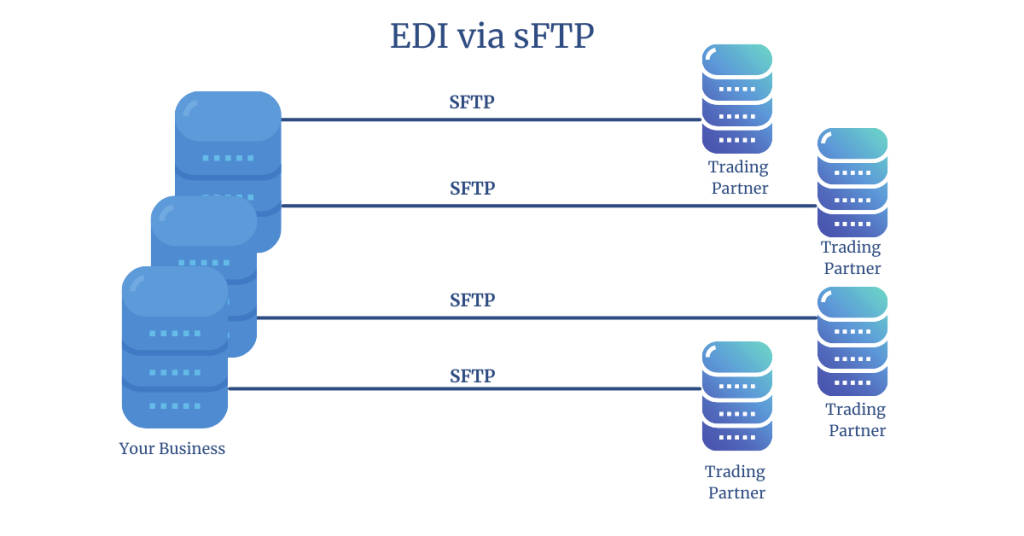
Secure File Transfer Protocol or sFTP can securely transfer files large and small, over the internet.
Secure File Transfer Protocol or sFTP is a network protocol that provides file access, file transfer, and file management over any reliable data stream. sFTP can securely transfer files large and small, over the internet. It builds on the File Transfer Protocol (FTP) and includes Secure Shell (SSH) security components. The security of SFTP file transfers is granted by leveraging SSH and encrypted FTP commands to avoid password sniffing and the exposure of sensitive information in plain text. Secure Shell (SSH) is a cryptographic component of internet security and SSH and SFTP was designed by the Internet Engineering Task Force (IETF) for greater web security. SFTP provides organizations with a higher level of file transfer protection which allows businesses to securely transfer important business documents.
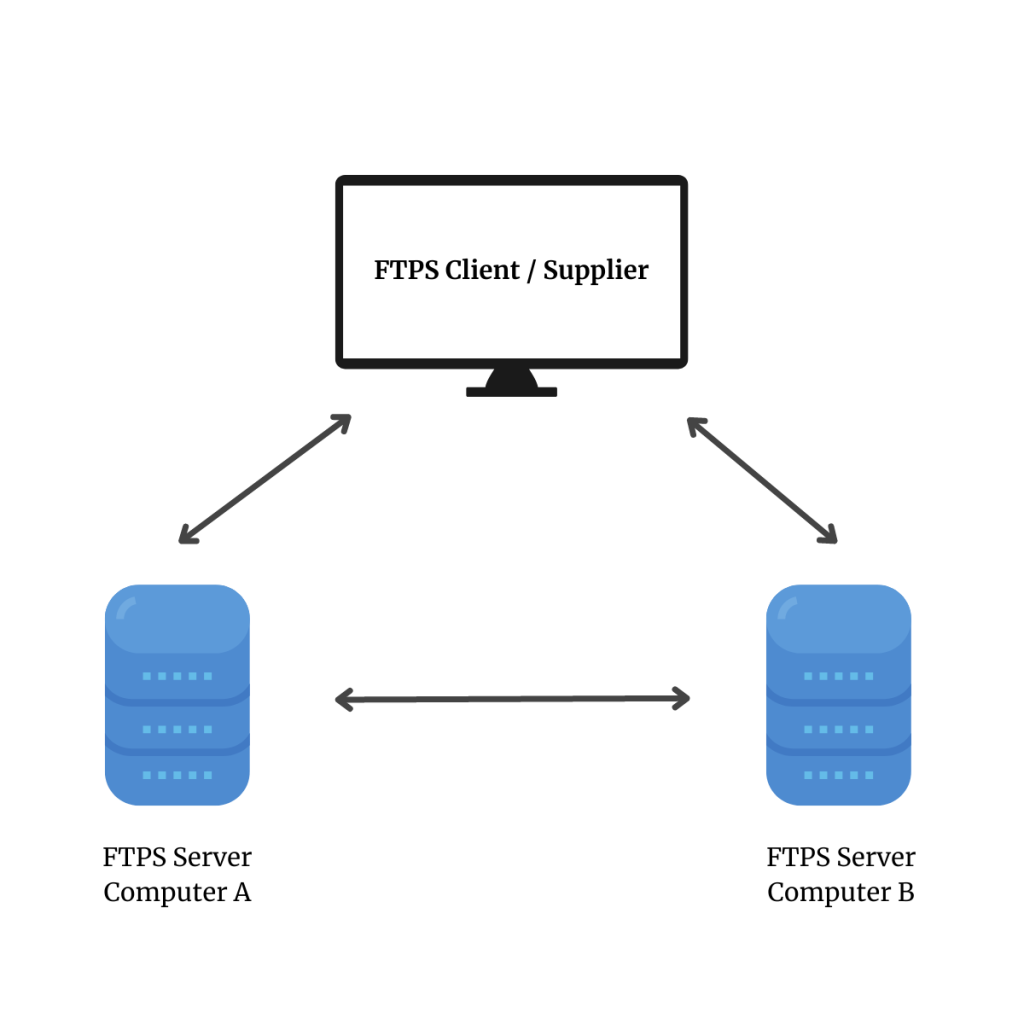
FTP stands for file transfer protocol, it is the most widely used communication protocol even today enabling connectivity via a TCP/IP network, such as the internet, to transfer files between two parties. FTP uses a client-server model which is secured through user credentials for authentication.
Advantages of Using FTP
AS2 stands for Applicability Statement 2 and it is one of the most popular methods for transporting B2B EDI documents from one organization to another.
AS2 is a second-generation communications protocol, created by the Internet Engineering Task Force (IETF) in 2002 to replace AS1. Today AS2 is used by millions of businesses worldwide, including many major retailers, such as Amazon and Walmart. AS2 protocol is designed with three core features Security, Integrity, and Non-Reputation
Security: Sensitive data is protected in AS2 through the transport layer which wraps EDI data in a secure “envelope” and sends it over the internet.
Integrity: The data is encrypted, and the identity of the sender and the integrity of the payload are ensured using pre-established digital certificates that are validated upon each connection.
Non-Reputation: The receiver of the data returns a signed message containing a Message Disposition Notification (MDN) confirming the successful transfer.
A simple AS2 setup involves two computers – a client and a server – connecting in a point-to-point manner via the web. Sending EDI documents via AS2 requires the receiving organization’s server to be always ‘listening”. Similar to a call to a phone without an answering machine, the message will be missed if the AS2 server is not available. As a result of this high availability requirement, many businesses prefer to use an EDI provider such as Commport to provide their AS2 connectivity. Supporting these types of high availability, technical requirements are Commport’s core business.

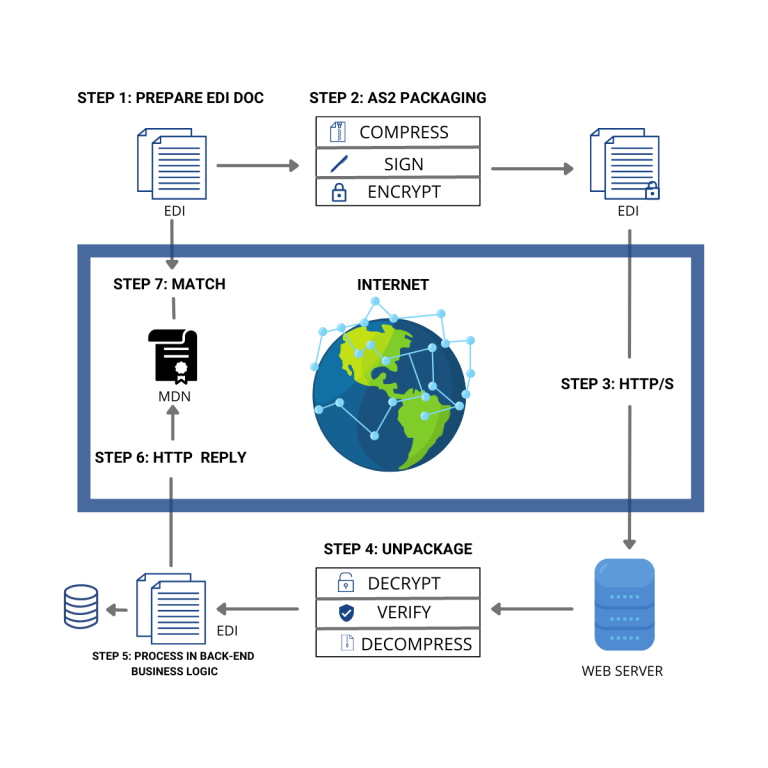
Step 1 – EDI Document Preparation
Documents are prepared in a standard EDI format to be sent over AS2
Step 2 – AS2 Packaging
The document is packaged to send via AS2 using three layers of transmission:
Compression – A document may be compressed using a compression algorithm to reduce the size of the data being transferred
Signature – Sender signs the document using the exchanged certificates and keys to ensure data integrity
Encryption – The data is typically encrypted using the receiver’s public encryption key, so only the proper recipient will be able to extract the document
Step 3 – Message Delivery
The data is transmitted securely over HTTP/S. A Message Disposition Notification (MDN) is returned to the sender confirming receipt.
Step 4 – AS2 Unpacking
Upon receiving the document at the receiver’s end, the document is decrypted using the receiver’s private key and then verified by using the sender’s public key and finally the document will be decompressed
Step 5 – EDI Processing
Step 6 – Confirmation of Receipt
The receiving organization uses AS2 or EDI software to extract the message and send message confirmation receipts such as the MDN and EDI functional acknowledgment (997) to the sender.
Step 7 – Sender Validation (MDN processing)
The sender receives the MDN and validates the receipt signature and completes any other configured data integrity checks that confirm the successful delivery transaction.
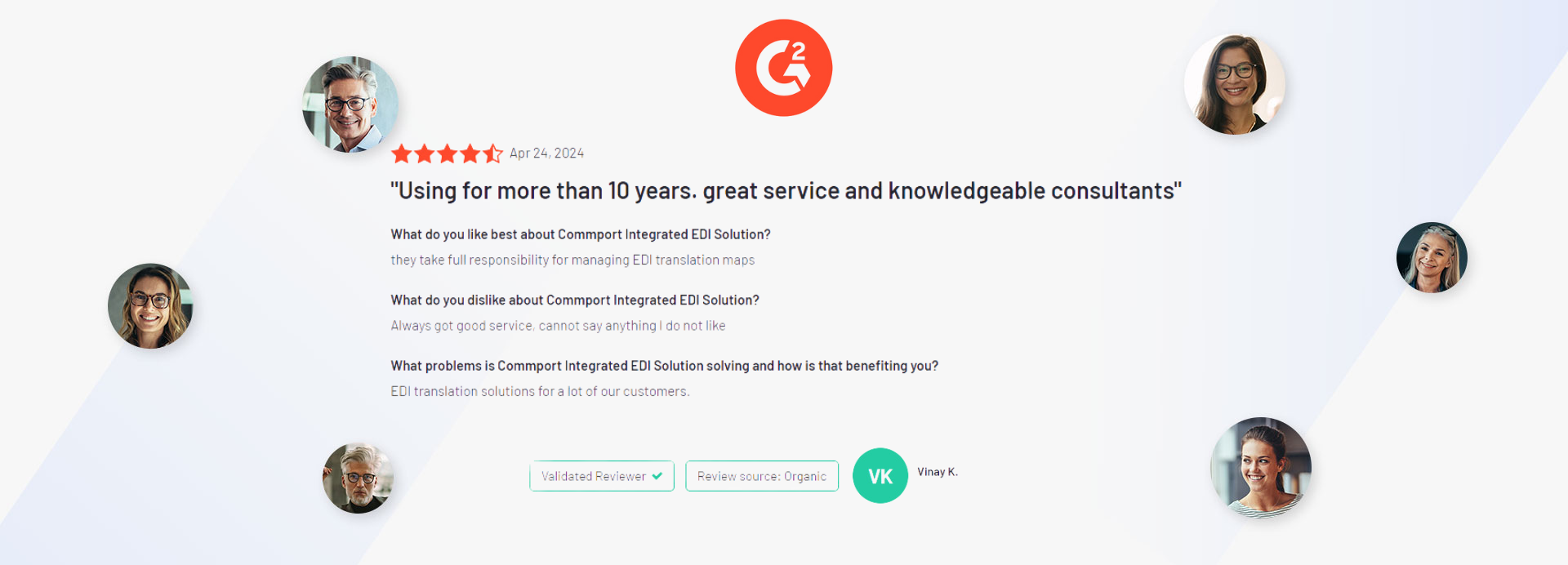
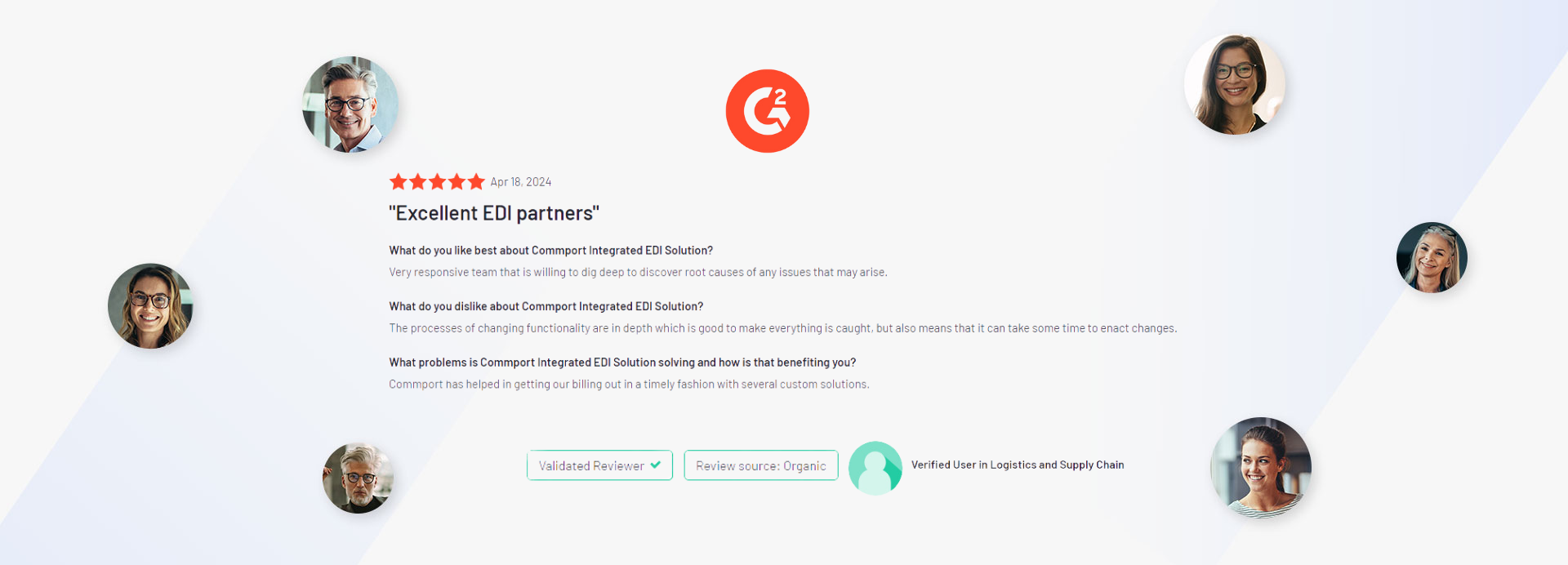
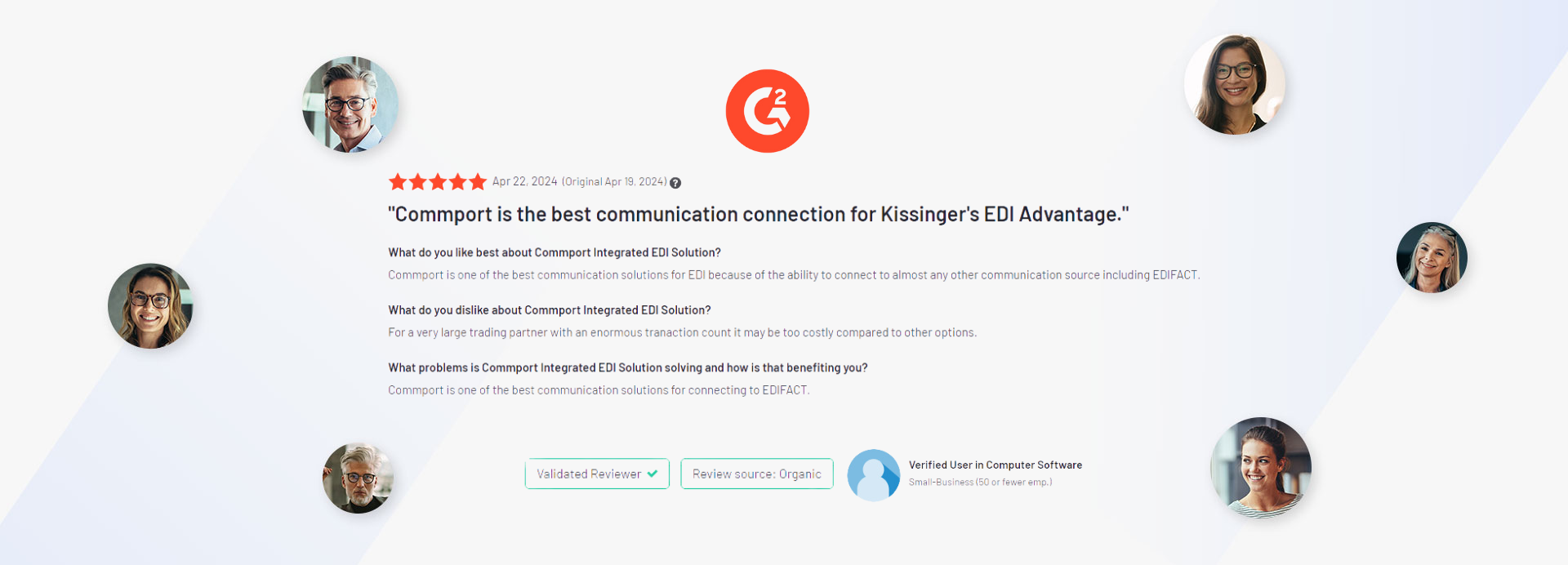
Discover the transformative impact of our EDI, CPS, and VAN solutions through the powerful testimonials of satisfied clients who have experienced remarkable results with Commport products and services.




Commport offers a secure and dedicated mailbox for each client which can be used to send and receive EDI messages 24/7.
VAN stands for Value-Added Network, which is a third-party service provider that facilitates the exchange of electronic data between trading partners. A VAN acts as an intermediary between businesses by providing a secure and reliable platform for transmitting electronic data, such as EDI messages, over the Internet or other networks.
FTP stands for File Transfer Protocol, which is a standard network protocol used for transferring files between computers over the Internet or other networks.
FTP provides a simple and efficient way to transfer files between a client and a server over a network. It uses a client-server architecture where the client initiates a connection to the server and can then upload or download files from the server.
sFTP stands for Secure File Transfer Protocol, which is a network protocol used for transferring files securely over a network. sFTP is a secure version of the File Transfer Protocol (FTP) and uses encryption to protect data in transit.
AS2 stands for Applicability Statement 2, which is a popular protocol used for secure and reliable data transfer between businesses over the Internet. AS2 is a specification developed by the Internet Engineering Task Force (IETF) that provides a standard method for exchanging electronic data using a secure and reliable transport mechanism.